Firewall Lab Setup : FortiGate
In the game of network security, you are either secure or you are not; there exists no middle ground.
If a computer is connected to the Internet connection, it is vulnerable to online attacks. The only difference is some computers could be more susceptible than others.
Table of Content
- Prerequisites
- What is Firewall
- Download FortiGate Virtual Firewall
- Configure Virtual network interfaces for FortiGate
- Deployment of FortiGate VM image in VMWare
- Configuring the Management Interface
- Accessing FortiGate Firewall GUI
- GUI Demonstration
- Dashboard Demonstration
Prerequisites
To configure the virtual FortiGate Firewall on your system there are some prerequisites required for installation
- VMWare Workstation
- FortiGate Firewall VM Image
- 3 or more NIC (Network interface cards) E1000 compatible network cards
- Root privileges
What is Firewall
In the computing language, a firewall is a security software or hardware that can monitor and control network traffic, both incoming and outgoing. It establishes a kind of barrier between reliable internal and unknown external networks.
Therefore, a firewall, also known as a network firewall, is capable of preventing unauthorized access to/from private networks.
A network firewall is based on security rules to accept, reject, or drop specific traffic. The firewall aims to allow or deny the connection or request, depending on implemented rules.
Download FortiGate Virtual firewall
First, we need to download the virtual FortiGate Firewall from the official FortiGate portal. To do this, visit here, and then register or login into the account.

By creating an account or log in to the account go to Download > VM Images as shown in the image below.

Further then Select Product: FortiGate > Select Platform: VMWare ESXi as shown in the image below. By default, you don’t have any license associated with your virtual image so, you can go with the trial version or you can buy the license as per your requirement.

After downloading the compressed FortiGate VM file you need to extract the compressed Zip file by using your favourite extractor and the extracted Zip file similarly looks like the below image.

Configure Virtual network interfaces for FortiGate
Let’s configure Virtual Network Adaptors as per your requirements.
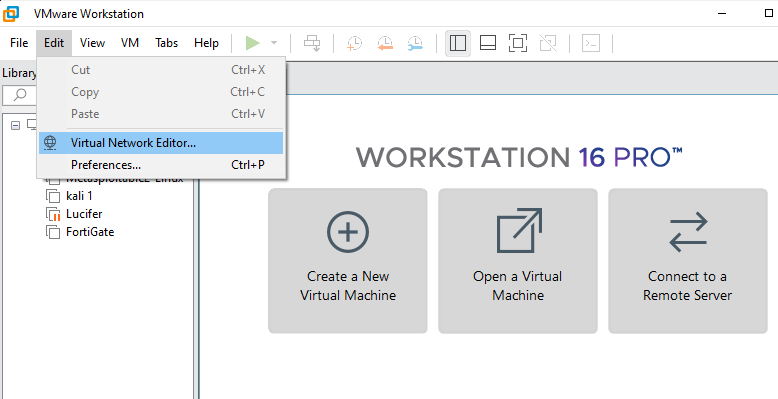
To do this open VMware then go to Edit > Virtual Network Editor as shown in the image below
Further, then it will open another prompt that allows you to modify the network configuration.
To make changes in network configuration it needs the Administrator privileges to provide Admin privileges click on change settings as shown below

Or also you can directly access the Virtual network editor app by click on Windows Start Button and search for Virtual Network Editor. If you are using Linux (i.e. Ubuntu) you can type the below command to open Virtual Network Editor.
sudo vmware-netcfg
By default, there are only two virtual network interfaces, i.e., VMNet1 and VMNet8. So, click on the Add Network and make your virtual interface host only. After that, you have to provide a unique IP address of network devices to each network interface.
For example, I am going to use 192.168.200.0/24 for the vmnet0 interface and so on…
Use Ip of your network devices or whatever as per your requirement. Similarly, you can add as much as network interfaces as you want but remember one thing all network configuration should be configured to Host-only and you can enable or disable DHCP service as per you system requirement

Deployment of FortiGate VM image in VMWare
Now it’s time to deploy the FortiGate virtual firewall in VMWare Workstation. Just open the VMWare Workstation and go to Files >> Open (Ctrl+O) or go to the Home tab and select open a virtual Machine. Select the FortiGate-VM64.ovf file that you have downloaded from the official Website of FortiGate as shown below

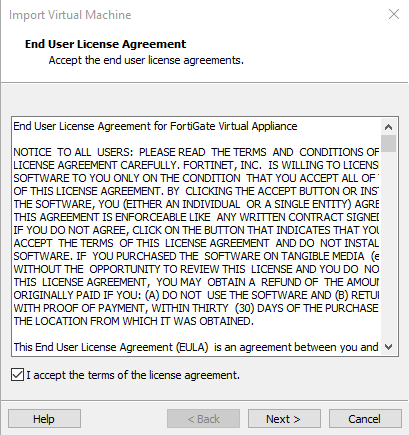
Then after it will open another prompt of End User License Agreement accept it and move to next
On the next prompt Assign a Name for the new Virtual machine and a Storage Path then after select import as shown below

This process going to take some time, so have patience. After the successful completion of this process,
Now it’s time to configure the Virtual Firewall resources by clicking on Edit virtual machine settings. just modify the assigned virtual network interfaces, memory, and processor by going to Edit virtual machine.

In my case, I’m giving 2GB RAM, 30 GB of Hard Disk, 1 Processor, and 6 different virtual network interfaces (VMNet2, VMNet3, VMNet4, VMNet11, VMnet11, VMnet12 to different network adaptors. Check the below image for reference.

Configuring the Management Interface
We’ve just finished the deployment process of the FortiGate Firewall in the VMWare workstation.
Let’s configure an IP Address to the management interface. In manner to assign an IP Address to management interface firstly, we need login to the system with default credentials
Login User: – Admin
Login Password: – In this circumstance, we don’t know the default password, Hit enter and change the password as shown below

Let’s check the system interfaces by running the following command
show system interface

Port 1 will be for the management interface so, assign a unique IP address to the management port and set to mode static. In this example our IP Address will 192.168.200.128/24 so, the default gateway will be 192.168.200.1. To assign IP Address to management port run the following command as shown below
config system interface edit port1 set mode static set ip 192.168.200.128 255.255.255.0 set allowaccess http https telnet ssh ping end

Also, we can verify the make changes of system interfaces by running the following command
show system interface

Accessing FortiGate Firewall GUI
Let’s check our firewall configuration by accessing the FortiGate Firewall GUI. Before accessing the GUI first, we will check the connectivity to our Firewall using the ping utility by running the following command
execute ping 192.268.200.128

As we can see the IP Address is reachable which means it is working properly now, we will access the FortiGate Firewall GUI using its management interface IP address.
https://192.168.200.128
use the same login credential that we have set up on CLI
Username: – admin
Password: – 123

By logging in to the firewall it will open a setup Prompt where we need to specify the Hostname, change password upgrade firmware, and Dashboard setup
By default, this FortiGate will use the serial number/model as its hostname. To make it more identifiable set a descriptive hostname as shown below

Already we have changed the password in Firewall CLI and also, we have already downloaded the latest version of the firewall, so it automatically skips you to the last step to Dashboard setup. Select it to Optimal or Comprehensive as per your requirements

After selecting the type of Dashboard hit ok and finish the setup.
GUI Demonstration
The GUI contains the following main menus, which provide access to configuration options for most FortiOS features:

Dashboard: – The dashboard displays various widgets that display important system information and allow you to configure some system options.
Security Fabric: – Access the physical topology, logical topology, audit, and settings of the Fortinet Security Fabric.
FortiView: – A collection of dashboards and logs that give insight into network traffic, showing which users are creating the most traffic, what sort of traffic it is, when the traffic occurs, and what kind of threat the traffic may pose to the network.
Network: – Options for networking, including configuring system interfaces and routing options.
System: – Configure system settings, such as administrators, FortiGuard, and certificates.
Policy & Objects: – Configure firewall policies, protocol options, and supporting content for policies, including schedules, firewall addresses, and traffic shapers.
Security Profiles: – Configure your FortiGate’s security features, including Antivirus, Web Filter, and Application Control.
VPN: – Configure options for IPsec and SSL virtual private networks (VPNs).
User & Device: – Configure user accounts, groups, and authentication methods, including external authentication and single sign-on (SSO).
WiFi & Switch Controller: – Configure the unit to act as a wireless network controller, managing the wireless Access Point (AP) functionality of FortiWiFi and FortiAP units. On certain FortiGate models, this menu has additional features allowing for FortiSwitch units to be managed by the FortiGate.
Log & Report: – Configure logging and alert email as well as reports.
Monitor: – View a variety of monitors, including the Routing Monitor, VPN monitors for both IPsec and SSL, monitors relating to wireless networking, and more.
Dashboard Demonstration
FortiGate dashboards can have a Network Operations Centre (NOC) or responsive layout.
- On a responsive dashboard, the number of columns is determined by the size of the screen. Widgets can only be resized horizontally, but the dashboard will fit on all screen sizes.
- On a NOC dashboard, the number of columns is explicitly set. Widgets can be resized both vertically and horizontally, but the dashboard will look best on the screen size that it is configured for.
Multiple dashboards of both types can be created, for both individual VDOMs and globally.
- Widgets are interactive; clicking or hovering over most widgets shows additional information or links to relevant pages.
- Widgets can be reorganized by clicking and dragging them around the screen.
Four dashboards are available by default: Status, Network, Security, and System Events
The Status dashboard includes the following widgets by default:
System Information: – The System Information widget lists information relevant to the FortiGate system, including hostname, serial number, and firmware. Clicking on the widget provides links to configure system settings and update the device firmware.
Licenses: – The License widget lists the status of various licenses, such as FortiCare Support and IPS. The number of used and available FortiTokens is also shown. Clicking on the widget provides a link to the FortiGuard settings page.
Virtual Machine: – The VM widget (shown by default in the dashboard of a FortiOS VM device) includes:
- License status and type
- vCPU allocation and usage
- RAM allocation and usage
- VMX license information (if the VM supports VMX)
Clicking on an item in the widget provides a link to the FortiGate VM License page, where license files can be uploaded.
FortiGate Cloud: – This widget displays the FortiGate Cloud and FortiSandbox Cloud status.
Security Fabric: – The Security Fabric widget displays a visual summary of the devices in the Fortinet Security Fabric.
Clicking on a product icon provides a link to a page relevancy to that product. For example, clicking the FortiAnalyzer shows a link to log settings.
Security Rating: – The Security Rating widget shows the security rating for your Security Fabric. It can show the current rating percentile, or historical security rating score or percentile charts.
Administrators: – This widget allows you to see logged-in administrators, connected administrators, and the protocols used by each Clicking in the widget provides links to view active administrator sessions, and to open the FortiExplorer page on the App Store.
CPU: – This widget shows real-time CPU usage over the selected time frame. Hovering over any point on the graph displays the percentage of CPU power used at that specific time. It can be expanded to occupy the entire dashboard.
Memory: – This widget shows real-time memory usage over the selected time frame. Hovering over any point on the graph displays the percentage of the memory used at that specific time. It can be expanded to occupy the entire dashboard.
Sessions: – This widget shows the current number of sessions over the selected time frame. Hovering over any point on the graph displays the number of sessions at that specific time. It can be expanded to occupy the entire dashboard.
The Security dashboard includes the following widgets by default:
- Top Compromised Hosts by Verdict: – This widget lists the compromised hosts by verdict. A FortiAnalyzer is required. It can be expanded to occupy the entire dashboard.
- Top Threats by Threat Level: – This widget lists the top threats by threat level,l from FortiView. It can be expanded to occupy the entire dashboard.
- FortiClient Detected Vulnerabilities: – This widget shows the number of vulnerabilities detected by FortiClient. FortiClient must be enabled. Clicking on the widget provides a link to view the information in FortiView.
- Host Scan Summary: – This widget lists the total number of hosts. Clicking on the widget provides links to view vulnerable devices in FortiView, FortiClient monitor, and the device inventory.
- Top Vulnerable Endpoint Devices by Detected Vulnerabilities: – This widget lists the top vulnerable endpoints by the detected vulnerabilities, from FortiView. It can be expanded to occupy the entire dashboard.
The System Events dashboard includes the following widgets by default:
- Top System Events by Events: – This widget lists the top system events, sorted by the number of events. It can be expanded to occupy the entire dashboard. Double click on an event to view the specific event log.
- Top System Events by Level: – This widget lists the top system events, sorted by the events’ levels. It can be expanded to occupy the entire dashboard. Double click on an event to view the specific event log.
Source: – http://docs.fortinet.com/document/fortigate/6.2.4/cookbook/856100/dashboard
Source: – geekflare.com/firewall-introduction/
Wait this is not the end ……
More will be discussed in the next part
Author – Vijay is a Certified Ethical Hacker, Technical writer and Penetration Tester at Hacking Articles. Technology and Gadget freak. Contact Here